Kelly Warner Law Firm Blames USA…
In what appears as a desperate attempt to defend multiple…
By – USA HeraldAaron Kelly Law Firm Resorts To…
Attorney Aaron Kelly and his law partner Daniel Warner are…
By – Jeff WattersonArizona Bar Opens Investigation on Attorney…
USA Herald recently reported on a developing story involving Attorneys…
By – Paul O'NealTrial Over Deadly Palisades Fire Reopens…
By Samuel López | USA Herald LOS ANGELES — Eighteen…
By – Samuel LopezFAA Issues Ground Stop at San…
SAN FRANCISCO – A sudden ground stop was issued for…
By – Tyler BrooksSynthesis: Bending Spoons Announces U.S. IPO
Milan-based tech powerhouse Bending Spoons has officially filed a registration…
By – Tyler BrooksDavid Grusch Returns To Capitol Steps…
By Samuel López | USA Herald Washington is about to…
By – Samuel LopezJeremy Corbell Issues UFO Warning: Release…
By Samuel López | USA Herald The war over government…
By – Samuel LopezSpirit Airlines Bankruptcy Sparks Outrage as…
By Samuel López | USA Herald As thousands of former…
By – Samuel LopezSpirit Airlines Bankruptcy Sparks Outrage as…
By Samuel López | USA Herald As thousands of former…
By – Samuel LopezDismantling Claims Before Discovery: How Operational…
By Samuel López | USA Herald Artificial intelligence has become…
By – Samuel LopezMusicians Declare War Over AI as…
By Samuel López | USA Herald The battle over artificial…
By – Samuel LopezChinese Company Blocked from Claiming Olympic…
By Samuel López | USA Herald The Olympic rings are…
By – Samuel LopezHoward Hughes Closes $2.1 Billion Insurance…
By Samuel López | USA Herald In a deal that…
By – Samuel LopezAmerica’s Legal Hiring Boom Is Here…
By Samuel López | USA Herald A quiet hiring boom…
By – Samuel LopezSkywatchers Events June 2026
Several meteor showers remain active throughout June. Skywatchers events also…
By – Jackie AllenSky Tonight App Highlights June 2026’s…
The Sky Tonight App is helping skywatchers make the most…
By – Jackie AllenDomestic Violence Deaths Remain High as…
Domestic Violence continues to claim lives across the United States…
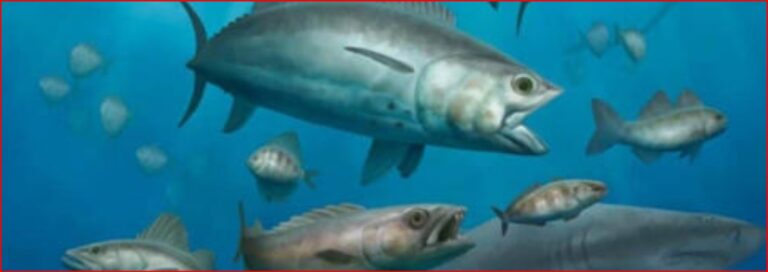
By – Jackie AllenQreiya 3 Fossil Discovery: Ancient Oceans…
Qreiya 3 is a remarkable fossil site which is providing…
By – Jackie AllenElevated Safety Posture Ordered for NASA…
An Elevated Safety Posture has been ordered for astronauts aboard…
By – Jackie AllenTaylor Swift’s Net Worth Reaches $2…
Taylor Swift’s net worth has climbed to an astonishing $2…
By – Jackie AllenTaylor Swift’s Net Worth Reaches $2…
Taylor Swift’s net worth has climbed to an astonishing $2…
By – Jackie AllenMysterious Death of Former Los Alamos…
The Mysterious Death of former Los Alamos National Laboratory employee…
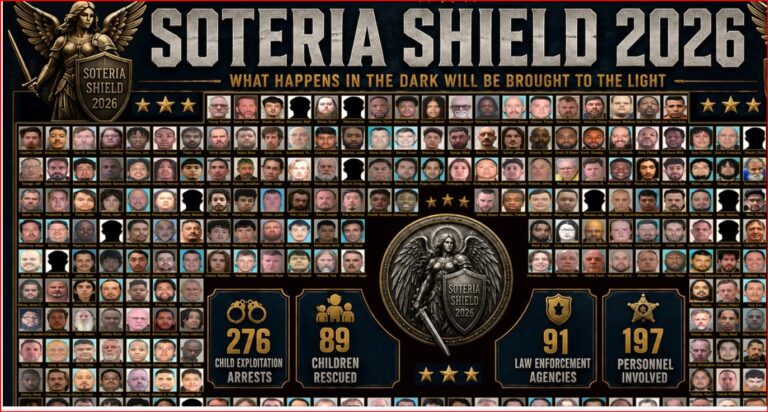
By – Jackie AllenOperation Iron Pursuit Leads to Hundreds…
Operation Iron Pursuit continues to generate significant results in the…
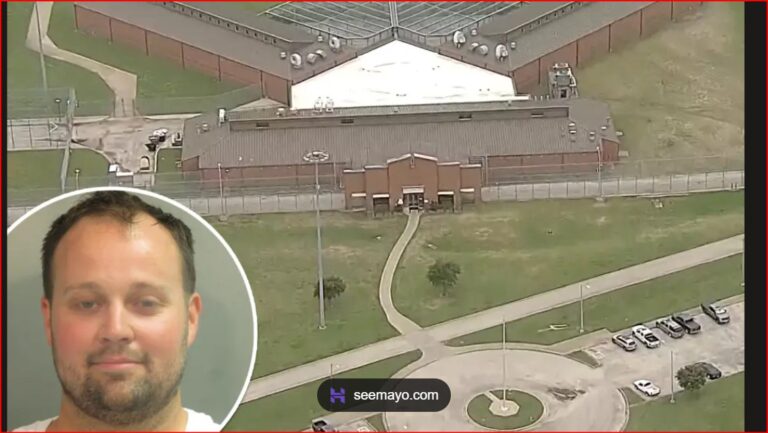
By – Jackie AllenJosh Duggar Appeal Denied as Convicted…
Josh Duggar remains behind bars after a federal judge denied…
By – Jackie AllenSleeping Dog Documentary Chronicles Jeremy Corbell’s…
The new documentary Sleeping Dog arrives at a pivotal moment…
By – Jackie AllenRare Blue Micromoon Lights Up the…
Skywatchers are in for a unique celestial event as a…
By – Jackie AllenAmerica’s Legal Hiring Boom Is Here…
By Samuel López | USA Herald A quiet hiring boom…
By – Samuel LopezLawsuit Aims to Knock Out Trump’s…
By Samuel López | USA Herald The fight may not…
By – Samuel LopezTrump Suggests Public Ownership of AI…
By Samuel López | USA Herald What if the next…
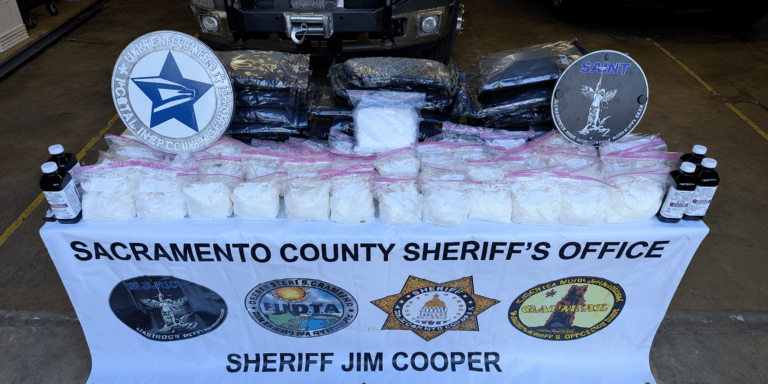
By – Samuel LopezOperation Spring Cleaning Delivers Massive Blow…
By Samuel López | USA Herald For three months, federal…
By – Samuel LopezNichelle Nichols’ Final Mission Ends in…
By Samuel López | USA Herald The woman who helped…
By – Samuel LopezIndia Police Raid Uncovers 100,000 Fake…
Indian law enforcement has seized more than 100,000 counterfeit credentials…
By – Samuel LopezCannabis Giants Hit with Sweeping Class…
A major class action filed May 4, 2026, accuses five…
By – Samuel LopezNew Pill Doubles Survival for Pancreatic…
Pancreatic cancer pill doubles life to 13 months By Tyler…
By – Tyler BrooksFDA warns public as cookie firm…
FDA warns public as cookie firm rejects urgent recall request…
By – Tyler BrooksTrump orders CDC to slash childhood…
Trump orders CDC to slash childhood vaccines from 17 to…
By – Tyler BrooksUSDA warns Americans over Salmonella in…
USDA warns Americans over Salmonella in meat products By Tylor…
By – Tyler BrooksAlien Coneheads: New DNA Study Doesn’t…
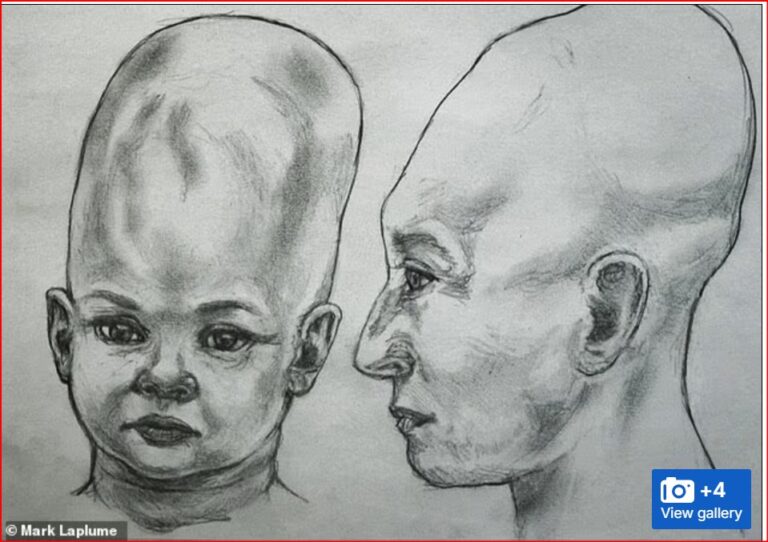
The mystery surrounding the so-called Alien Coneheads of Peru has…
By – Jackie Allen2026 Stanley Cup Final Game 2:…
2026 Stanley Cup Final Game 2: A Thrilling Comeback The…
By – Tyler BrooksSupreme Court signals 27 states could…
Supreme Court signals 27 states could ban trans female athletes…
By – Tyler BrooksMauricio Pochettino sounds alarm on Chris…
Mauricio Pochettino sounds alarm on Chris Richards injury By Tylor…
By – Tyler BrooksUSMNT star Chris Richards tears two…
USMNT star Chris Richards tears two ankle ligaments By Tylor…
By – Tyler Brooks“Money” Mayweather Tucks Tail: $100 Million…
Floyd Mayweather has beaten every opponent who ever climbed into…
By – Samuel LopezMackenzie Shirilla Sent Text Messages to…
Mackenzie Shirilla is once again at the center of public…
By – Jackie AllenNo posts found.
No posts found.